
Data Loss Prevention (DLP) safeguards sensitive information by identifying, monitoring, and blocking unauthorized access or transfers. Modern DLP evolved from complex legacy systems to AI-driven, endpoint-aware tools protecting PII, IP, and regulated data. A successful DLP strategy combines clear policies, user education, and integration with broader security frameworks. Netwrix Endpoint Protector strengthens this with advanced endpoint and content-aware protection.
This guide is your go-to resource for understanding and using Data Loss Prevention (DLP) in your organization. It covers what DLP is, how it has evolved, and how it stands apart from other security tools.
You’ll learn what types of sensitive data DLP protects, from personal details to intellectual property, and the challenges of identifying them. The guide also explains the differences between data loss, leaks, and breaches, breaks down key DLP features, and offers practical strategies to build a strong DLP program.
Key Takeaways
- DLP’s core role: Prevents data loss, leaks, and unauthorized access by identifying, monitoring, and securing sensitive information. Ensures data integrity, availability, and compliance.
- DLP evolution: From early 2000s point solutions to AI-driven, cloud-integrated platforms. Legacy DLP was complex and rigid, while modern solutions offer automation and real-time protection.
- What DLP Protects:Sensitive data like PII (e.g., SSNs, financial records), intellectual property (source code, trade secrets), and regulated data (NIST,PCI DSS, GDPR, HIPAA).
- Implementation strategy: Effective DLP requires clear policies, employee training, access controls, and integration with security frameworks.
- Adoption Drivers: Cyber threats, stricter regulations, remote work, and the cybersecurity talent gap are pushing organizations toward more scalable, user-friendly DLP solutions.
1. What is DLP?
Definition: Data Loss Prevention (DLP) is a technology that helps prevent data breaches and unauthorized data transmission.
1.1 What Does DLP Do?
- Identifies Sensitive Data: DLP tools help you recognize what data needs extra protection.
- Prevents Data Loss: Monitor and block data transfer and exfiltration, whether accidental or intentional.
1.2 Industry Definitions
- Forrester: Detects and prevents violations to corporate policies regarding the use, storage, and transmission of sensitive data.
- Gartner: Classifies and inspects content across multiple platforms and applies policies dynamically.
1.3 How is DLP Different from Other Security Tools?
DLP is not a one-size-fits-all solution, but part of a broader cybersecurity strategy that may include:
- Antivirus Software: Fends off malicious programs.
- Web Security: Detects vulnerabilities in your web applications.
- Intrusion Detection: Identifies suspicious network activity.
Key Takeaway: While other cybersecurity tools offer generalized protection, DLP specifically focuses on data identification and loss prevention.
2. History and Evolution of DLP
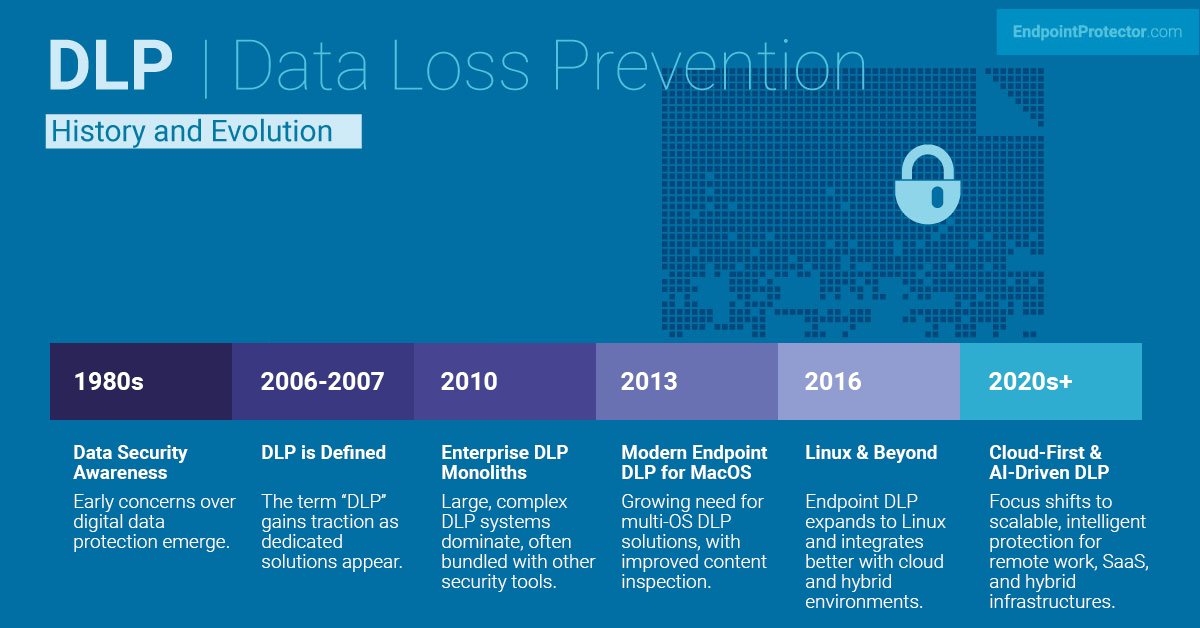
2.1 A Brief Timeline
- 1980s: Data security starts to gain attention.
- Early 2000s: Specialized DLP solutions emerge.
- 2006-2007: The term “DLP” is coined and popularized.
2.2 Early Concepts
The first mentions of DLP date back to the early part of this century. According to a 2008 SANS Institute paper, the term “DLP” gained traction in 2007, although its functionalities were partially available in other software prior to that.
2.3 The PGP Milestone
In 1991, Phil Zimmermann developed Pretty Good Privacy (PGP), one of the first solutions focusing on data protection and a foundational element of data encryption. Its primary purpose was to secure email messaging through asymmetric encryption.
2.4 The Age of DLP Monoliths: Early 2010s
DLP solutions around 2006 and 2007 quickly evolved into complex systems. They were either absorbed by software giants or became standalone, intricate monoliths. These solutions relied heavily on complex regular expressions for data identification, which became a challenge for security teams.
2.5 The Problem with Monoliths
Big market players offered these bulky DLP solutions as part of larger software bundles. While these were readily bought by enterprises, they often proved too cumbersome to manage. Default settings were inadequate for diverse environments, leading to significant data slips.
2.6 Evolution: Two Different Approaches
- Niche Integration: Some vendors integrated DLP into specialized cybersecurity products, like email security solutions. However, this often resulted in subpar data identification.
- Focused Technologies: Others concentrated on specific aspects of DLP, such as endpoint and user activity monitoring, ensuring top-notch data identification and protection against unauthorized transmission.
3. Types of Data: What DLP Protects
3.1 The Dilemma of Definition
Defining what constitutes “sensitive data” can be difficult, given its variability across different contexts. For instance, commercial application source code can be highly sensitive, while the same code in an open-source setting is not. This ambiguity often results in false positives.
3.2 Universal Types of Sensitive Data
While the definition of sensitive data can differ, some types are universally recognized, and often governed by laws:
- Personally Identifiable Information (PII): Primarily defined in the United States, PII includes data that can trace an individual’s identity – name, Social Security number, and biometric data, among others.
- Personal Data: A broader term, especially in the context of Europe’s General Data Protection Regulation (GDPR), encompassing any information related to an identifiable person, like location data or online identifiers.
- Sensitive Personal Information (SPI): Defined under the California Privacy Rights Act (CPRA), this term may extend to include IP addresses, which are generally not considered PII or Personal Data.
- Nonpublic Personal Information (NPI): Originating from the Gramm-Leach-Bliley Act (GLBA), NPI could include names, income, credit scores, and even data collected via cookies.
3.3 Intellectual Property
Aside from personal data, businesses often need to protect various types of intellectual property (IP):
- Source Code: Especially important in software development.
- Formulas: Crucial for industries like pharmaceuticals.
- Diagrams, Videos, and More: Varied forms of intellectual assets critical to different business types.
3.4 The Complexity of the Task
DLP security faces a challenging task, considering various definitions and scopes of data depending on local laws and the nature of the business. This is why fixed rules often fall short, and machine learning algorithms play a critical role in identifying sensitive data.
4. Understanding Data Loss, Data Leaks, and Data Breaches: Key Differences

4.1 Data Loss: The Starting Point
DLP software primarily aims to prevent data loss, which can occur in two main ways:
- Data Exposure: Data is moved out of your controlled environment, either intentionally or unintentionally, without necessarily being a result of a cyberattack.
- Source-Level Data Loss: Losing data at the source, like a hard drive failure where there is no backup. This scenario is usually outside the purview of DLP software.
4.2 Data Leaks: The Endpoint
A data leak (or data leakage) can be understood in terms of where the data ends up:
- External Malicious Access: Data is accessed by an outsider through hacking or system vulnerabilities.
- Intentional Leaks: This happens when someone inside or outside your organization intentionally transfers sensitive data to unauthorized locations.
4.3 Data Breaches: Malicious Intent
A data breach usually refers to:
- Unauthorized Access: A cyberattack resulting in unauthorized access or disclosure of sensitive, confidential, or protected data.
4.4 The Terms in Context
- Data Loss: Focuses on the source or origin of the missing data.
- Data Leak: Centers on the destination that the data reaches.
- Data Breach: Highlights the unauthorized and often malicious intent behind the data exposure.
4.5 Summary: Use of Terminology
Though these terms are often used interchangeably, their usage depends on intent, source, and effect. They all essentially refer to the situation when sensitive data “gets out.” Using the terms interchangeably shouldn’t be a cause for concern, as they all focus on aspects of the same overarching issue.
5. DLP Core Features: An In-Depth Look
DLP software serves a crucial role in safeguarding sensitive data, working in real-time to monitor, identify, and prevent unauthorized transmission. Let’s delve into the core features that make DLP indispensable.
5.1 Sensitive Data Identification: The Foundation
- Traditional Methods: Earlier DLP software relied on fixed rule sets, requiring constant updates by administrators as new data types emerged.
- Modern Approaches: Utilizing machine learning and statistical analysis, contemporary DLP software learns over time to better identify sensitive data and reduce false positives.
5.2 Endpoint-Focused DLP: User Workstations
- Data Matching: Monitors clipboards and other activities on user’s personal computers and laptops to identify sensitive data.
- Real-Time Actions: Blocks data pasting to risky locations like instant messaging apps or social media sites, while allowing for secure internal application usage.
- Media Control: Prevents or encrypts data being transferred to external storage like USB drives.
5.3 Transmission-Focused DLP: Network and Cloud
- Protocol Monitoring: Acts much like a firewall, observing network traffic in real-time through multiple protocol gateways.
- Traffic Control: Instantly blocks any sensitive data detected in HTTP, SMTP, FTP, and other Internet protocols.
- Cloud Integration: Modern DLP solutions have expanded their scope to include cloud storage environments, adapting to today’s data storage needs.
5.4 Summary: Multi-Faceted Protection
While the overarching goal is to identify and secure sensitive data, different DLP solutions may specialize in particular channels of data loss. Whether focusing on endpoints or data transmission, modern DLP systems leverage advanced technologies to provide robust, adaptive, and real-time data protection.
6. The DLP Policy Framework: Beyond Technology

While DLP technology plays an essential role in safeguarding sensitive information, it is only a part of a comprehensive DLP policy framework. Let’s examine the crucial components that make up a complete and effective DLP strategy.
Strategic Foundation: What is a DLP Policy Framework?
A DLP policy framework serves as your strategic blueprint, outlining your approach to DLP across various phases. It complements your tactical DLP program, focusing on the hands-on aspects of DLP.
Phase 1: Planning Your DLP Strategy
- Preparation: Before even considering a DLP solution, thorough planning is essential. This includes organizing training sessions, drills, webinars, and educational exercises.
- Data Classification: Quality DLP tools can help automate this, but human judgment is required to assess data sensitivity levels and to define access controls.
- Compliance and Audits: Familiarize yourself with relevant regulations like HIPAA, PCI DSS, and GDPR, and plan for internal and external audits as needed.
Phase 2: Implementing Your DLP Measures
- Data Sanitization: Prioritize cleaning up sensitive data that are unnecessary or stored in inappropriate locations.
- Access Controls: This is the time to set up and evaluate data access and exchange permissions, leveraging insights from existing data access logs.
- Software Configuration: Beyond just setting up the DLP software, focus on configuring it to meet your specific needs.
Phase 3: Ongoing Maintenance and Monitoring
- Continuous Monitoring: Data access should be continuously monitored to revoke any unnecessary permissions and to identify new types of sensitive data.
- Account Management: Especially important in scenarios like staff turnover, account permissions must be constantly updated.
- Incident Preparedness: Maintain an up-to-date reaction and remediation plan to ensure you are prepared for any data loss incidents.
While technology is a vital enabler, a well-thought-out DLP policy framework ensures that you are not solely dependent on it. By paying equal attention to planning, implementation, and ongoing maintenance, you create a robust and adaptive strategy to protect your organization’s valuable data.
7. Crafting a Robust DLP Program: A Tactical Guide
The DLP program acts as the operational arm of your overarching DLP strategy. While the specifics may vary depending on an organization’s unique structure, needs, and data types, there are universal elements crucial for success. Here’s a breakdown of key components you should incorporate into your DLP program.
7.1. Employee Education and Awareness: The First Line of Defense
- Importance: DLP effectiveness starts at the human level. Educated employees are less likely to make errors that lead to data loss.
- Case Study: Boeing’s 2017 incident serves as a cautionary tale. Lack of awareness led to the loss of personal data for 36,000 employees and a subsequent hefty fine.
- Action Items: Conduct regular training sessions, quizzes, and simulations to instill a culture of data awareness.
7.2. Compliance with Data Security Best Practices: The Security Foundation
- Principle of Least Privilege: Start by ensuring that only those who need access to sensitive data have it. It’s easier to grant access later than to revoke it after the fact.
- Action Items: Conduct regular audits to ensure the principle is being followed. Immediately revoke unnecessary access and regularly update access protocols.
7.3. Integration with Broader Security Measures: A Holistic Approach
- Why It’s Essential: DLP shouldn’t operate in isolation. It must be part of a comprehensive security framework to be effective.
- Common Pitfalls: Even robust DLP solutions falter if other aspects of security are weak. For example, vulnerable web apps can render DLP useless, making data breaches imminent.
- Action Items: Regularly update and test all security measures, including web application security, firewalls, and intrusion detection systems.
A successful DLP program isn’t just about implementing software solutions; it’s about creating a culture of awareness, adhering to cybersecurity best practices, and integrating DLP into a broader security framework. By covering these key areas, you can develop a DLP program capable of adapting to evolving risks and safeguarding your organization’s data assets effectively.
8. The Evolving Landscape of DLP Adoption: Trends and Imperatives

In an age where digital footprints are expanding, organizations of all sizes find themselves in the intricate web of data protection. Here’s a comprehensive look at the key trends and driving forces behind the growing adoption of DLP solutions.
8.1. The Ubiquity of Sensitive Data: A Shared Challenge
- The Reality: From customer emails to credit card information, businesses of all sizes deal with sensitive data daily.
- The Risk: This data is becoming an increasingly lucrative target for cybercriminals.
8.2. The Surge in Digital Vulnerabilities: A Race Against Time
- Growing Concerns: With more systems digitized, the risk of identity theft and unauthorized access to systems is escalating.
- Non-Traditional Threats: Beyond organized cybercrime, novice hackers are entering the field, enabled by user-friendly ransomware packages and cryptocurrencies.
8.3. The Cybersecurity Talent Gap: A Looming Crisis
- The Challenge: A shortage of skilled cybersecurity professionals exacerbates the vulnerabilities organizations face.
- Adoption Drivers: This gap is pushing businesses to search for automated solutions that can compensate for human resource limitations.
8.4. The Role of MSSPs: A Double-Edged Sword
- SMBs’ Go-To: Small and medium-sized businesses often outsource cybersecurity to managed security service providers (MSSP).
- MSSP Challenges: Like their clients, MSSPs grapple with skills gaps, budget limitations, and escalating customer demands.
8.5. The DLP Market Dynamics: A Shifting Terrain
- Traditional Solutions Falling Short: Legacy DLP systems are increasingly deemed inadequate, as underscored by Gartner’s decision to retire its Magic Quadrant for Enterprise DLP.
- The Road Ahead: Organizations are pivoting towards more efficient, cost-effective, and easy-to-manage DLP solutions.
The drive for adopting DLP solutions is complex, influenced by ever-evolving risks, a growing talent gap, and a dynamically changing market. Organizations must stay agile, informed, and proactive in their approach to effectively protect their digital assets in this challenging landscape.
9. Why Endpoint Protector?
Endpoint Protector by CoSoSys has established itself as a specialist player that provides best-in-class endpoint DLP and Device Control. It focuses on the most sensitive area of potential data loss – the end users.
In addition to offering modern data classification technologies with statistical analysis and machine learning, Endpoint Protector helps you make sure that your users don’t share your sensitive data outside and don’t transport it in an insecure way. This helps you protect against data loss due to the activity of malicious insiders as well as unintentional cases due to errors and negligence. Not only does Endpoint Protector secure and monitor data, but it also helps meet compliance requirements.
Frequently Asked Questions
Download our free ebook on
Data Loss Prevention Best Practices
Helping IT Managers, IT Administrators and data security staff understand the concept and purpose of DLP and how to easily implement it.















