
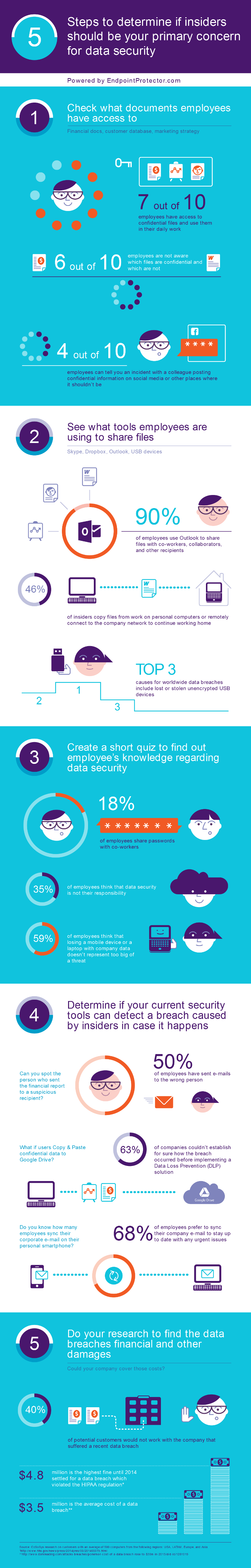
Recently we conducted a research on our customers to have a more clear idea on the employees’ behavior in relation to company data and we have made some interesting discoveries.
1. Pretty much all employees have access to confidential data and the majority of them don’t even know it
7 out of 10 employees work with financial information, Personal Identifiable Information, marketing plans, customer databases, you name it. To prevent data breaches, a significant number of businesses rely solely on the confidentiality agreement that people sign when they get hired. But they do not realize that those agreements do not guarantee that people will not disclose confidential data by negligence. If 6 out of 10 people are not aware which files are confidential and which are not, you can imagine that they wouldn’t have a problem copying a contract to their personal e-mail address to finish reading it at home.
2. Outlook is the most popular tool for file sharing
Even though we suspected this, it is interesting to actually have a statistic. 90% of employees use Outlook to share files with co-workers, collaborators and other recipients. This means that if a breach were to happen, chances are to happen on Outlook especially because 50% of the respondents have admitted to send e-mails to the wrong person.
Another important finding was that USB devices are not yet obsolete. People still find them convenient and efficient to transfer data rapidly. With USB 3.0 standard the transfer speed has increased (ten times faster than USB 2.0) and of course, since a few years ago, the storage capacity is no longer a problem. Now, the use of USB devices at the office to transfer files or to take work home is not a problem. The problem intervenes when people lose them and there is no protection for stored data. Lost or stolen unencrypted USB devices are among top 3 causes for worldwide data breaches.
3. Employees’ knowledge regarding data security scares us more than a horror movie
We are strong promoters of a sound training program for employees to be included in the data security plan. We always said that no security tool can do its magic without proper involvement of the human part. Still, there are companies where 35% of the employees think that data security is not their responsibility and 59% of employees think that losing a mobile device or a laptop with company data doesn’t represent too big of a threat. Training programs should be taken more seriously and they should be approached in a fun and interactive way so people can relate and understand better why data security is important and their role in it. Gamification and simulations of possible data breach scenarios could be viable solutions.
4. Data Loss Prevention is as important for audit than it is for prevention
Our research revealed that 63% of companies couldn’t establish for sure how a breach occurred before implementing a Data Loss Prevention (DLP) solution. Practically, they couldn’t say what employee copied confidential files to Google Drive, sent them by Skype, by e-mail, etc. or if it was even the case of a breach caused by an insider. How can you prevent a breach if you cannot find the cause of a previous one? This is where DLP helps. On one side, businesses can setup policies to prevent data losses, on the other side, if a breach occurs (no DLP is bulletproof), they have reports that can indicate policy violations.
5. The costs of a data breach imply more than just money
A breach can bring irreparable damages and among those, there is the image. In our research, 40% of the respondents said they would not work with the company that suffered a data breach. Losing the customers and potential customers’ trust is like a death sentence for any business. Reestablishing trust is a matter of reinventing the company and spending lots of money for campaigns to reposition the company in their audience eyes.
And…because we like to play around with statistics, we created also an infographic based on the results of the research. Enjoy and until the next article, stay safe!
Download our free ebook on
Data Loss Prevention Best Practices
Helping IT Managers, IT Administrators and data security staff understand the concept and purpose of DLP and how to easily implement it.















