
Here we are, at the end of another great year for the cybersecurity world. Along the year, we’ve witnessed some unpredictable events, but also the evolution of data loss prevention.
No one can argue that Data Loss Prevention (DLP) as a concept and technology has come a long way since it emerged in 2006. Back then it disrupted the security industry with the capabilities of identifying and blocking sensitive data from leaving the company, which no other solution could have done. It was a great innovation also due to USB control features that stopped employees from copying sensitive data to USB devices, strengthening companies’ data security. Since 2006, the DLP adoption increased exponentially and now, there is no IT security professional that hasn’t heard about this great IT security tool.
But let’s get back to the year 2016. It is a perfect moment of the year to look back and see how has DLP evolved in the last year. What changed? How is it now perceived by companies? Have DLP implementations increased in 2016 and what’s next for it?
2015 was the year of major data breaches that boosted the demand for DLP, and 2016 had its fair share of breaches. Remember the biggest data breach so far of Yahoo, Snapchat, Oracle, IRS, Yahoo!, Dropbox, LinkedIn and many others. While not all were the result of an insider job, the human factor is extremely important, like in Snapchat’s data leak involving an employee willingly sending payroll information to an attacker who posed as his boss. Incidents like these have shaped Data Loss Prevention as we know it today – context oriented, content analysis driven, less intrusive, intuitive, efficient.
2016 has also been the year of Slack. Wherever you turned around, there was someone working with Slack, therefore, DLP vendors made their first steps to a deeper integration with cloud services for messaging, collaboration and file sharing. That is the future, experts say. People need to work smarter, not harder and that means fast access to resources, regardless of the location, efficient means of communication, and minimal interaction with the IT department for approval to use certain apps. On the other hand, businesses and IT departments also started to request more often a more flexible model for DLP, a model that doesn’t require investing in additional infrastructure items, one that allows IT administrators to manage permissions and see logs and reports from any Internet connected computer. Thus, Data Loss Prevention as a Service became popular, aligning to the industry trend for Cybersecurity as a Service.
A lot has changed also for endpoint DLP when it comes to supported operating systems, driven of course, by the changing infrastructures, which are still Windows dominated, but with a significant increase in macOS and Linux computers as well. If in the previous years, you could see only solutions for Windows networks, in 2016, cross-platform solutions for macOS and Linux have been released. We launched the version for Macs in 2013 and the expertise gained so far from implementations and customer feedback made our DLP solution, Endpoint Protector 4, the most advanced one available on the market. In 2016, we released the Content-Aware DLP solution for Linux as well, supporting now cross-platform networks with Windows, macOS, and Linux within the same management console.
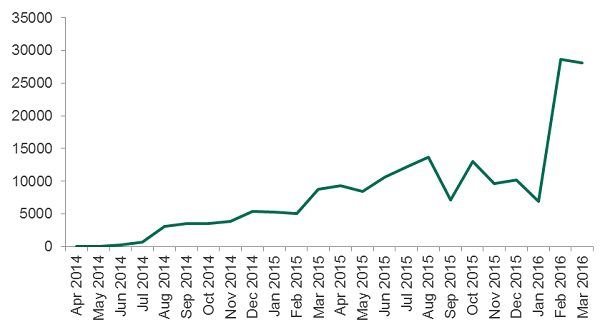
More companies have implemented DLP in 2016? You bet. While reports with the market size have not been yet published, we notice over 30 percent in worldwide Google searches for Data Loss Prevention, with the same percentage of growth for our customer number. The growth is determined by different factors, among which the fact that DLP purchasing motivation has shifted from compliance to protection of Intellectual Property, business records, and employee’s records. The perception of DLP has also changed, companies acknowledging that this technology has evolved and it isn’t so difficult, heavy, and cumbersome and vendors have made progress in that direction.
What’s next in 2017 in the dynamic world of IT security?
Smarter DLP
We are confident that researchers’ predictions saying that, by 2018, ninety percent of organizations will implement at least one form of integrated Data Loss Prevention, up from 50 percent today, will come true. Technically, the solution to prevent data leakages and theft will take the form of an AI-driven tool, with machine learning techniques – which have already started to be seen in the market – and with advanced user behavior analytics.
These will enhance the solution’s capabilities to accurately identify sensitive data, it will decrease false positives, and successfully stop data losses. The integration with cloud services will also be richer and it will focus more on the data stored by apps to tackle the issue directly at the source.
Increasing attacks on mobile devices
The number of mobile devices is continuously growing, being expected to reach 4,77 billion in 2017. Just think about the winter holiday and the fact that mobile devices and other gadgets are among the top gifts that will most surely be brought to work! IT departments will have a serious challenge at the beginning of the year to protect the new devices connected to their network against possible data security threats.
Internet of malicious things will expand
WiFi and Internet-connected devices will generate 68 percent of all internet traffic by 2017.
Last year, the number of connected devices estimated for 5 years was 39 billion, while it has been predicted that the IoT devices will exceed 46 billion in 2021, a 200 percent increase from this year. Along with the booming growth of IoT devices, malicious devices and cyber-attacks will increase.
More businesses will use cloud-based services
With more regulations and compliance requirements, more businesses will use the cloud because of the improved security features. Many will adopt the BYOD policy, allowing employees to use wearables and IoT connected devices supported by cloud applications and solutions.
Increase in home-attached devices
New home security systems, wireless cameras, and other smart home-attached devices emerge daily on the market. Unfortunately, most of them don’t have a solid built-in security, becoming a target for attackers.
More organizations will invest in data security
With the GDPR regulation coming into force in May 2018, organizations will invest more in data security in order to avoid highly cost fines that could have a big damage on the business and to fulfill their need of monitoring their users’ activity and ensure sensitive data is not leaked or lost.
Large-scale security breaches
Many areas, like transportation, logistics, and healthcare only recently adopted IoT, so they are more vulnerable to data threats, data leakage or theft. Without a strong security solution, they easily become targets of cyber criminals.
All in all, the threat landscape looks “promising”, with more entry channels for external attackers, as well as exit points for insiders, challenging organizations, and vendors. The good news is everybody strives to learn from their mistakes or others’ and time passing by makes us all wiser, as people and professionals, contributing to a more secure world.
Have an inspiring Holiday Season! Stay secure, stay happy!
Download our free ebook on
Data Loss Prevention Best Practices
Helping IT Managers, IT Administrators and data security staff understand the concept and purpose of DLP and how to easily implement it.















