
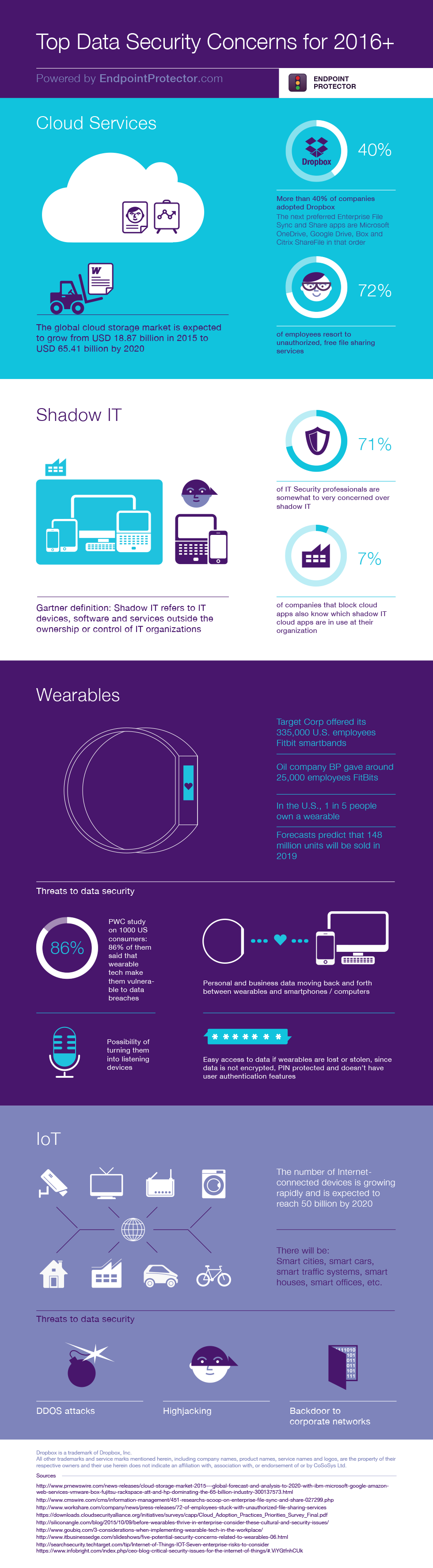
Statistics about Cloud Services, Shadow IT, Wearables, and IoT show that they are amongst the top data security concerns for organizations. Now, more than ever, apps and interconnected devices are part of our lives and, with data moving back and forth between wearables and smartphones / computers, it is no wonder organizations are becoming more vulnerable.
Cloud services like file sharing tools, social media, etc. are a top data security concern for many organizations due to the fast adoption among employees who use them for easy collaboration and uploading / copying files. Most of the time, these services and applications are not authorized by IT departments but through a Data Loss Prevention solution, businesses have the option to limit data transfers only to trusted web addresses.
Shadow IT is a concern for 71% of security professionals, being justified by the fact that uncontrolled apps and services can lead to data security incidents due to human error and unauthorized data transfers.
Another concern which has only recently begun to get its claws out is represented by wearables. A PwC study revealed that 86% of 1000 US consumers think that wearable tech makes them vulnerable to data breaches. This is because their most intimate details, like hours of sleep, heart rate, consumed calories, business apps data, etc. are collected by wearables and it is uncertain what it is being done with them. The truth is wearables vendors do not have as a top priority the development of security features. They are more focused on innovative features that provide more options to make devices more appealing for the consumers.
If you want to find out more about wearables and what you can do to protect collected data, you should read this article on Before wearables thrive in the enterprise, consider these cultural and security issues.
The Internet of Things (IoT) makes way for what may be the breakthrough of this century, but also one of the biggest risks for data security since it implies bigger structures like entire cities. In case of a data security incident, you can imagine the disaster that would fall upon a city, with inter-connected systems. For smaller structures like homes or cars, data security vulnerabilities could be life-threatening.
Find out interesting statistics about these concerns in the infographic below.
Download our free ebook on
Data Loss Prevention Best Practices
Helping IT Managers, IT Administrators and data security staff understand the concept and purpose of DLP and how to easily implement it.













