Using Cryptographic HashesBeing a data security vendor, we value the integrity of the files you receive. Endpoint Protector provides cryptographic hashes on product download pages to ensure you deploy the correct files. Checksums algorithms count the number of bits in the transmission for the purpose of detecting errors which may have been introduced during its transmission or storage. The MD5 and SHA256 hash sums provide a highly unique fingerprint in this regard, enabling you to verify that the downloaded files are unaltered from the original.
To confirm the file integrity, use the Terminal or a SHA and/or MD5 utility tool to calculate the hash for the files downloaded from Endpoint Protector website. If the hash you calculated matches the one we provided, you can be certain of the downloaded file’s integrity. SHA and MD5 utilities are available for Windows, Mac and Linux.
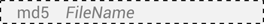
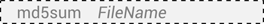
Calculating MD5 and SHA on LinuxMost Linux distributions provide an MD5 and a SHA256 command for calculating message digests:
 Calculating MD5 and SHA on Windows
Calculating MD5 and SHA on WindowsThere are several tools available for Windows but File Checksum Integrity Verifier (FCIV) can be used. Please see additional details on FCIV at
https://support.microsoft.com/en-us/kb/841290Calculating MD5 and SHA on MacA command line is also available for Mac OS X. Although there are several options, depending on the OS version, some might not work. The best way for calculating message digest: