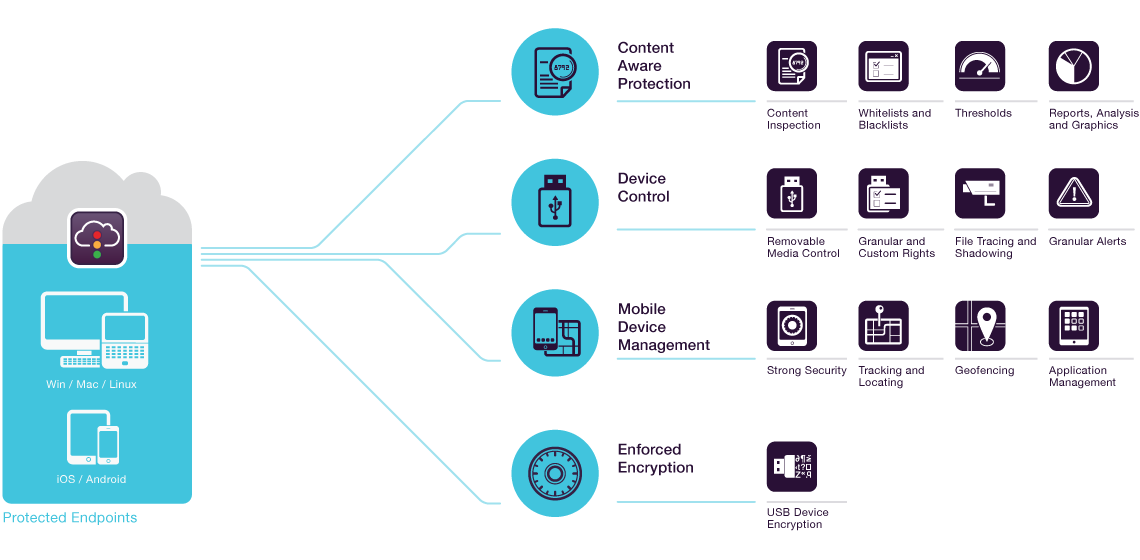
My Endpoint Protector - 100% cloud-managed DLP
Protect your organization's sensitive data and eliminate the threats posed by portable storage devices, cloud services, and mobile devices. My Endpoint Protector is a full Device Control, Data Loss Prevention (DLP) and Mobile Device Management (MDM) cloud-based solution available for Windows, macOS and iOS and Android mobile devices. Portable storage devices such as USB flash drives, tablets, e-mail applications like Outlook, and cloud services like Dropbox, iCloud, Google Drive, etc. may cause severe issues when it comes to controlling the use of confidential data. With My Endpoint Protector, you can minimize the risks of data loss, data theft, and data leakage and also manage the mobile device fleet from a single centralized online console from anywhere, at any time.
Content Aware Protection
For Windows and macOS
It offers detailed control over sensitive data leaving the computers and endpoints in the network. Through efficient content inspection, transfers of critical company documents will be logged and reported. Based on the company policy, file transfers will be allowed or blocked.
Device Control
For Windows and macOS
Having the possibility to control USB devices and peripheral ports activity from a simple web interface will make things easier. Strong device use policies will ensure proactive protection for a safer work environment with removable storage devices.
Mobile Device Management
For Android, iOS, and macOS
It offers enhanced control over the use of the Android and iOS mobile device fleet. MDM features are also available for Macs. Enforce strong security policies and access detailed tracking and asset management of all smartphones or tablets. Increase productivity by monitoring and pushing applications, network settings, and more.
100% Cloud-Managed
Software as a Service
Controlling ports and USB devices, confidential data and mobile devices in the cloud is the best solution to centrally manage your network without having to become an IT expert.
My Endpoint Protector Highlights
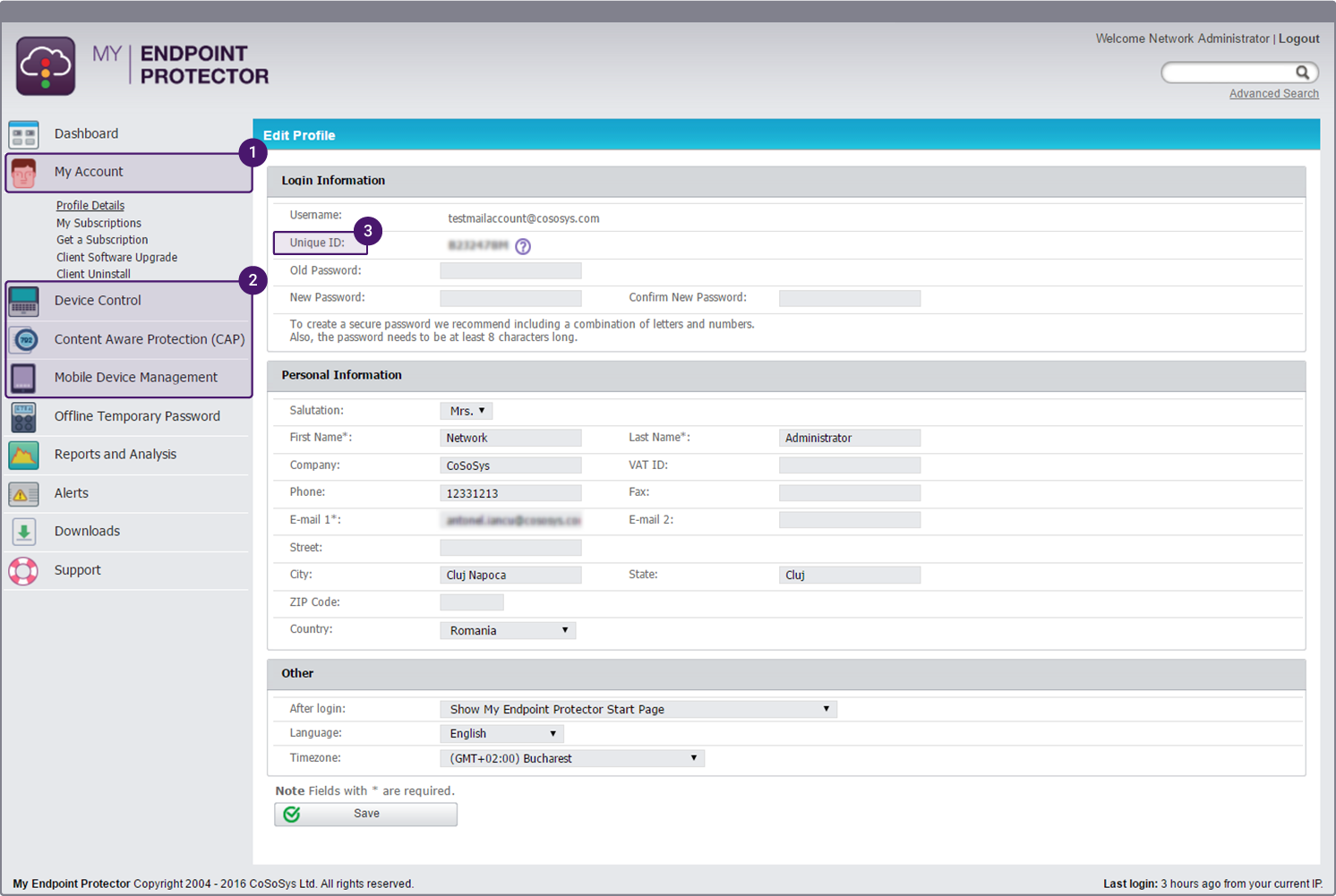
1
An intuitive DLP and MDM solution, managed from a cloud-based interface, offering simple and easy access to subscription management, profile details, client software installation files and upgrade options.
2
Device Control, Content Aware Protection, and Mobile Device Management are the three modules united in the most advanced cloud-managed DLP and MDM solution.
3
For the security of your account, you receive a Unique ID. It is an important part of the account, being mandatory when installing the My Endpoint Protector client / agent on a new computer.
How My Endpoint Protector Works